The latest phishing attack to come to our attention takes the form of a non-delivery notification from Office 365, which takes you to an external site set up to gather data and steal your login credentials.
We want everyone to be as prepared as possible for this sort of threat, from our internal staff to our loyal clients, so we’ve gathered together as much information as possible to keep you updated and alert.
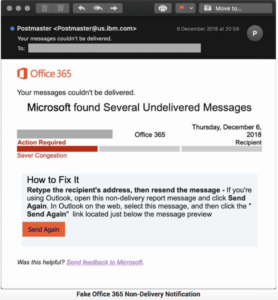
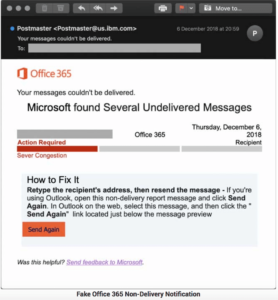
This latest attack, discovered by ISC handler Xavier Mertens, opens with the statement that ‘Microsoft has found several undelivered messages’ and encourages you to click a link to resend the emails that are supposedly awaiting delivery.
The attack is designed to fool users, gain access to legitimate email inboxes, and use them for a variety of malicious activities.
The design and interface of the attack are pretty subtle, mimicking Microsoft’s emails and platform design to a decent degree of detail. The link in the email takes you to a phishing site tricked up as a Microsoft login page, which requires your login details to continue.
If you do end up entering your password, your credentials will be forwarded to a separate javascript function while you are redirected to the legitimate Microsoft login page, meaning you might not even be aware that something is up.
As always, we can’t stress strongly enough how important it is to be certain you are on the right sites when you input your login details. Always check the email addresses of messages asking you to click links or input information, and double-check suspect URLs before giving up any information.