Targeting over 133 countries, eleven thousand IP addresses, and deploying over sixty-two thousand phishing emails, the ransomware, dubbed .locky, is currently wreaking havoc on a global scale.
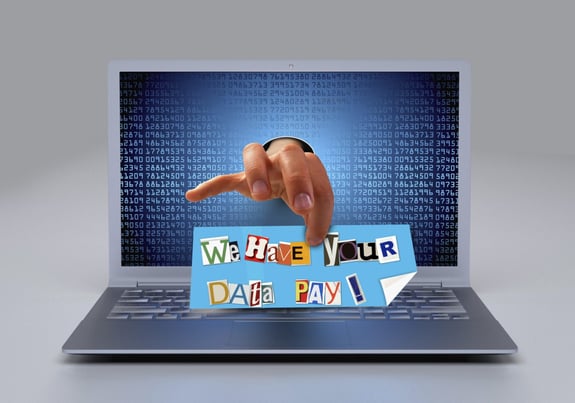
So, what is ransomware?
There are two types of ransomware; 1) it encrypts the files on a computer or network. 2) it locks a user's screen. Both types require users to make a payment (the 'ransom') to be able to use the computer again.
How does ransomware infect your system?
By clicking unknown attachments, links, or programs. Even visiting some types of websites can make you vulnerable to a ransomware attack. Other ways can be transfer via memory sticks or USBs of an infected machine or through social engineering like Facebook messenger.
What impact does ransomware have?
Ransomware will prevent access to your system or data until a solution is found.
The security vendor Comodo said in a statement, “The campaign was first detected on Aug. 9, and more than 62,000 phishing emails related to the attack were detected at Comodo-protected endpoints alone, as of Friday.”
Therefore, it is important to know a couple of ways to spot phishing emails. Phishing (pronounced just like “fishing”) is not unlike fishing itself. Thieves and scammers send out a line (an email) with a hook (promise of money or threat of action) hoping to catch a fish (personal information or money).
Examples of Phishing Emails
Phishing emails appear to come from a reputable source. Some common ones include Canada Revenue Agency, PayPal, Apple, or even your bank. They generally look very authentic and include logos, and the sent-from address looks to be from that organization. They include a link to another site.
When looking at an email, make note of the following things:
- Is it addressed to you by name, or does is it generic (sir/madam, client, customer, staff, subscriber, friend, or just your email address)?
- Phishing emails are generally addressed generically. If they use your name, ensure it is spelled correctly.
- Are there numerous spelling and/or grammar errors?
- Phishing emails generally have several spelling or grammar errors and may read poorly.
- Is there a link in the email? If you hover over the link, is the URL which displayed the same as what is written in the email?
- A phishing email will type out a reputable-looking URL, but if you hover over it and look at the URL that pops up, it is different.
- Is there an inherent threat in the email?
- Phishing emails often include a threat such as your account will be locked or blocked, or you may face retribution such as fines or jail (popular with the Canada Revenue Agency phishing emails)
- Is there a promise which seems to be good to be true?
- Some phishing emails include promises of money.
With .locky continuing its destructive path, now is a good time to review if your organization is receiving proper back-ups, that there is a security plan in place, and that all users have education about ransomware and phishing emails.
Stay safe out there.